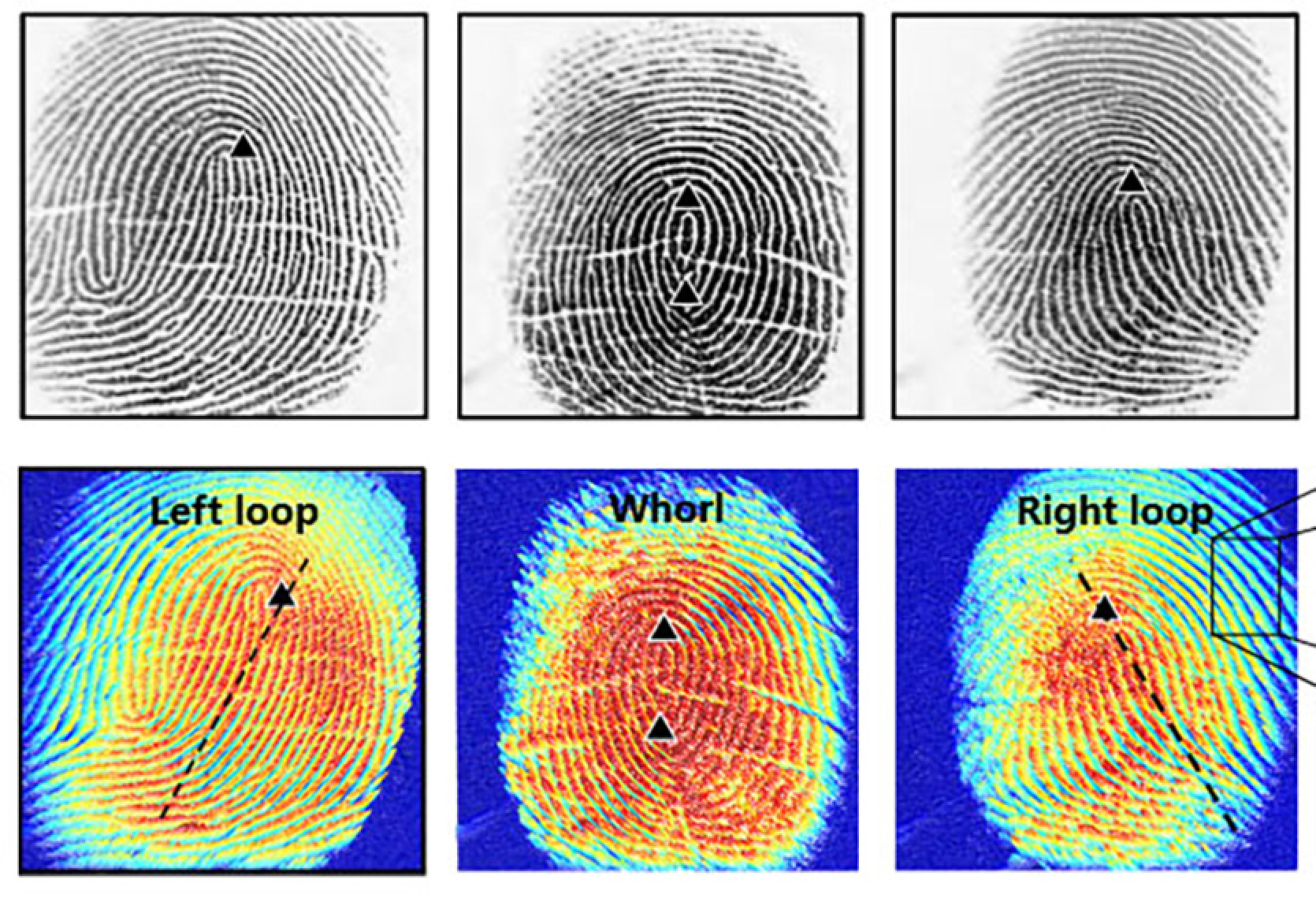
A research group from the USA and China has uncovered a new threat associated with biometric authentication. Their work is titled "PrintListener: Detecting Fingerprint Authentication Vulnerabilities through Finger Friction Sounds". The attack leverages the sound characteristics of the user's finger movement to extract fingerprint template features.
After tests, researchers claim they can successfully recover up to 27.9% of partial fingerprints and 9.3% of full fingerprints within five attempts. This is the first work to use finger sounds to gather information about fingerprints.
Biometric fingerprint authentication is widely used and trusted. However, organizations and individuals are increasingly aware that malefactors might want to steal their fingerprints. Some have started to be cautious about exposing their own fingerprints and hand details in view and photos.
How can malefactors establish fingerprints through sound? Any communication software working with an active microphone can pose a danger: Telegram, Skype, Discord, and the like.
The PrintListener attack is complex, but scientists managed to overcome several issues hindering the desired result:
- Weak finger friction sounds - an algorithm for sound localization based on spectral analysis has been developed
- The dependence on separating finger pattern from user's physiological and behavioral characteristics - largely overcome by minimum redundancy maximum relevance (mRMR) techniques and adaptive weighting strategies
- Transition from primary fingerprint features to secondary ones - achieved through statistical analysis of relationships between these features and a heuristic search algorithm
PrintListener uses a series of algorithms for preprocessing raw audio signals, which are then used to create target synthetics for PatternMasterPrint (MasterPrint, created from fingerprints with a specific pattern).
Importantly, PrintListener has undergone numerous experiments "in real-world scenarios" and, as mentioned in the introduction, can lead to successful partial fingerprint attacks in more than every fourth case and complete fingerprint attacks in almost every tenth case. These results significantly outperform dictionary fingerprint attacks.
Source: Tom's Hardware










Comments (0)
There are no comments for now