In the popular xz Utils package for lossless data compression and working with the .xz format, a backdoor was discovered. A backdoor is a method of bypassing standard authentication procedures, providing unauthorized remote access to a computer.
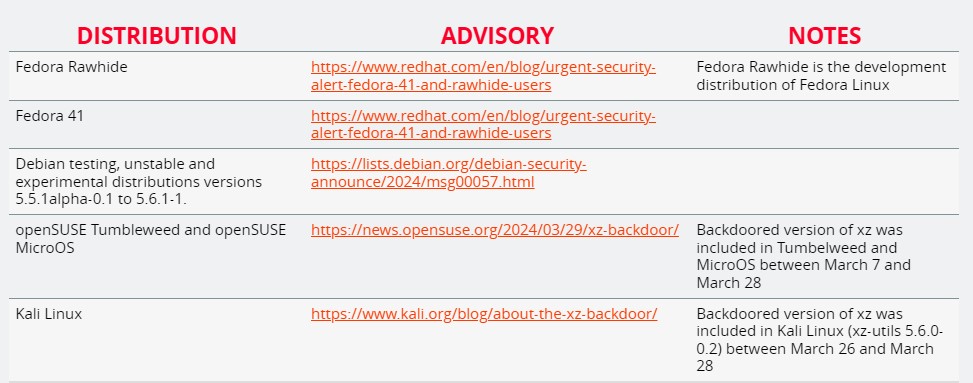
On Friday, users urged to immediately stop using Fedora 41 version 5.6.0 and Fedora Rawhide version 5.6.0 or 5.6.1 distributions.
Suspicions exist regarding other distributions. However, at the moment, there is no confirmation.
ArsTechnica detailed the incident.
xz Utils
XZ Utils is a set of free programs for data compression. It is included in every Linux distribution and other Unix-like operating systems.
xz Utils provides critical functions for compressing and unpacking data during all kinds of operations.
What happened?
The problem was first noticed by developer Andrey Froind, who works on Microsoft PostgreSQL proposals. Recently he was addressing performance issues with SSH in the Debian system, a widely used protocol for remote access to devices via the Internet.
In particular, SSH access was heavily loading the CPU and generating valgrind memory monitoring errors.
Eventually, he discovered that the issues were a result of the xz Utils updates. The developer officially reached out to the Open Source Security List and stated that the updates resulted from someone intentionally installing a backdoor in XZ Utils.
What does the backdoor do?
The malicious code added to xz Utils versions 5.6.0 and 5.6.1 changed the software's operation during runtime operations.
When these functions involved SSH, they allowed executing malicious code with root privileges. It enables someone with a predefined encryption key to access the backdoor system via SSH.
Thus, the person would have the same level of control as any authorized administrator.
The backdoor was in the making for years
Experts noted that creating the backdoor took more than one year.
In 2021, user JiaT575 first participated in an open-source project.
In hindsight, changes in the libarchive project raised suspicions as they replaced the safe_fprint function with a variant that was long considered less secure. However, this went unnoticed at the time.
The following year, JiaT575 submitted a fix to the xz Utils mailing list, and soon an previously unnoticed participant joined the discussion, claiming that xz Utils developer Lasse Collin had not updated the software in a long time.
This pressure led to JiaT575 joining the project.
In January 2023, he first participated in the development. And in the subsequent months, he allegedly became more and more involved in the process.
- JiaT575 replaced Collin's contact information with his own in Microsoft's oss-fuzz, a project that scans open-source software for signs of malicious intent.
- He also disabled the ifunc function during testing. This allowed the security system to ignore the changes made.
- In February 2024, JiaT575 issued commits for versions 5.6.0 and 5.6.1 of xz Utils. The updates implemented the backdoor.
In the following weeks, Tan and others urged Ubuntu, Red Hat, and Debian developers to add updates to the system. Some were expected to be released soon.
The backdoor is implemented using a five-stage loader that uses a series of simple but clever methods to conceal itself. It also provides means for delivering new payloads without requiring significant changes.













Comments (0)
There are no comments for now